introduction: as the demand for cross-border services and localized testing increases, taiwan’s native ip has become a common resource. this article introduces the ways to obtain taiwan’s native ip, acceptable anti-blocking strategies, and high-level ideas on traffic camouflage from a compliance perspective, focusing on risk control and legal compliance.
legal ways to obtain taiwan’s native ip
to obtain taiwan’s native ip, you should first choose legal channels, such as cooperating with taiwan’s local network service providers, renting taiwan computer room nodes, or purchasing hosting nodes through compliant agency service providers. avoid using ip or gray services from unknown sources to avoid legal risks and reputational risks.
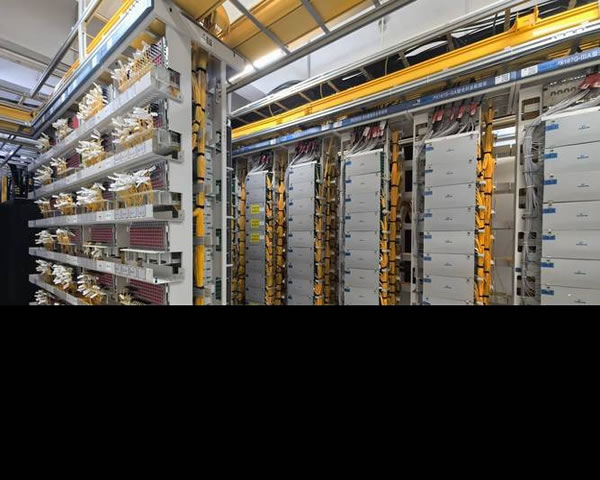
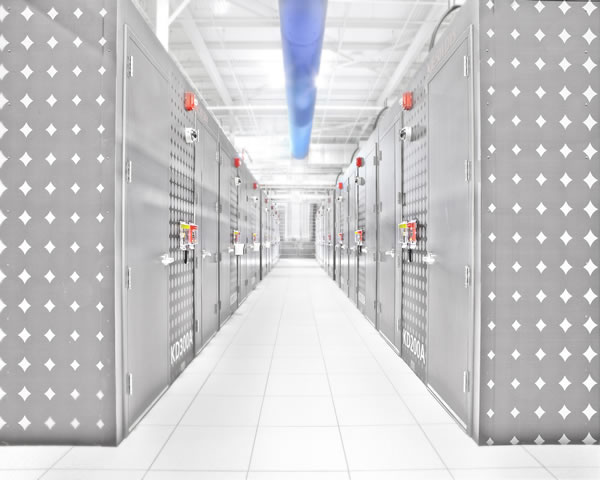
carrier and data center hosting
hosting directly in a data center in taiwan or contracting with a local operator is the most reliable way. such solutions usually provide fixed public network ip, bandwidth guarantee and contract terms, which help to prove compliance and long-term stability, and are suitable for enterprises that require long-term localized ip.
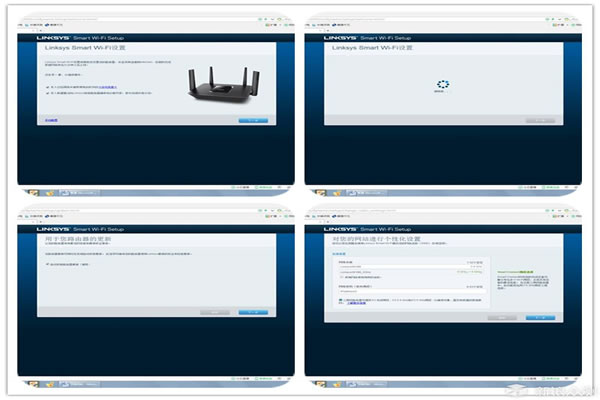
legal agent and cloud node service
nodes set up by compliance agents and cloud service providers in taiwan can provide on-demand elastic ip or proxy pools. when choosing, you should review the service agreement, audit and compliance certificates to confirm that it does not involve traffic resale or mixed ash production, so as to reduce the possibility of being blocked or legally held accountable.
compliance considerations and risk control
when using taiwanese native ip, you must consider laws, terms of service and privacy protection. establishing contract and audit chains, keeping log compliance policies, and passing legal and compliance team assessments before use can effectively control compliance risks and subsequent disputes.
anti-blocking strategy (high-level, legal direction)
anti-blocking strategies should focus on good architecture and compliant operations: reasonably disperse traffic, cooperate with service providers, whitelist cooperation and identity authentication, and adopt reasonable session and rate control to avoid abnormal access patterns to target services.
connection and session management
stable session management and connection policies can reduce the risk of traffic being determined to be abnormal. persistent sessions, a reasonable number of concurrent connections, and session behavior compatible with the target system should be used, and access patterns should be recorded for subsequent analysis and processing.
rate limiting and backoff strategies
external requests should follow the throttling and backoff principles: adjust concurrency and frequency according to the allowable rate of the target service, implement exponential backoff and alert when encountering rejection or exception, to avoid bans or complaints caused by continuous high-frequency detection.
legal uses and technical boundaries of traffic masquerading
"traffic disguise" is mostly used in legal scenarios for privacy protection, compliance testing or to bypass unreasonable censorship. acceptable methods include standardizing http headers, enabling tls, forwarding through legal proxies, etc., but they must not be used to circumvent legal review or infringe on third-party rights.
legal traffic optimization and privacy protection methods
reasonable traffic handling includes using a cdn or reverse proxy to optimize latency, using end-to-end encryption to protect user data, minimizing logs and personal information within the scope of the law, while ensuring user knowledge and consent to comply with regulations.
sensitive implementation details (declarations) not provided
for security and compliance reasons, this article does not provide any specific implementation steps, scripts, or configurations to avoid blocking, evading detection, or bypassing security mechanisms. if technical implementation is required, please evaluate and implement it through a legal and compliant solution provider or an internal security team.
summary and suggestions
in short, when building or using taiwanese native ip, compliance and transparency should be the premise, priority should be given to formal channels and a complete risk control and audit mechanism should be established. regarding anti-blocking and traffic camouflage, we only discuss high-level architecture and legal optimization, and do not recommend any practices to circumvent laws or terms of service. if you need to implement it, it is recommended to consult a compliance lawyer and a qualified network service provider to jointly develop a plan.

- Latest articles
- Cost Analysis: Is There A Comparison Of The Costs Of Renting And Purchasing Cloud Servers In Vietnam?
- German Cloud Server Hosting Image Selection And Rapid Deployment Tips For Developers
- Comparison Of Rent And Bandwidth Costs Helps Determine Where The Game Room In Thailand Is More Cost-effective
- Cost And Billing Model Analysis Teaches You How To Save Money By Buying Alibaba Cloud Thailand Servers
- Buying Guide How To Choose The Suitable Hong Kong Native Ip Hong Kong Cn2 Provider And Price Comparison
- Recommendations For Regional Selection: Bandwidth And Latency Differences In Different Cities For Server Rental In Thailand
- Integration Solution: How To Access Korean Native Ip Query Url To The Automated System To Achieve Batch Query
- Evaluation Summary Of Packet Loss Rate And Jitter Of Three Networks Cn2 Malaysia In Real Business Scenarios
- How To Configure Ci Cd And Monitoring Alarm System For Hong Kong Server From A Developer Perspective
- Actual Cases Share The Optimization Effect Of 2k Servers In Japan On Cross-border Business
- Popular tags
-
Comprehensive Analysis Of The Construction And Management Skills Of Taiwan's Native VPS IP
Comprehensively analyze the construction and management skills of Taiwan's VPS native IP to help users use VPS services efficiently. -
Introduction To The Working Principle And Application Of Taiwan’s Native Ip Proxy
gain an in-depth understanding of how taiwan native ip proxies work and their application in network security and data privacy. -
Performance Analysis And Application Scenarios Of 8km Servers In Taiwan
This article will analyze the performance of Taiwan’s 8km servers and discuss its application scenarios to provide reference for users to choose a suitable server.